When a WAF Blocks One XSS Payload but Misses Another: Why Cloud-Based Filtering Is Not a Complete XSS Defense
Introduction
In web application security, one of the most common misconceptions is that a Web Application Firewall (WAF) can “solve” Cross-Site Scripting (XSS). In practice, a WAF may detect and block many known attack patterns, but it is not a substitute for secure application design, correct output encoding, and context-aware input handling.
This post documents a real-world style observation: one XSS attempt was blocked by an upstream protection layer, while a different variation still resulted in script execution. The goal of this write-up is not to provide a bypass recipe, but to explain why this happens, what defenders should learn from it, and how engineering teams should respond.
During initial testing, one reflected XSS attempt was stopped by the upstream protection layer.
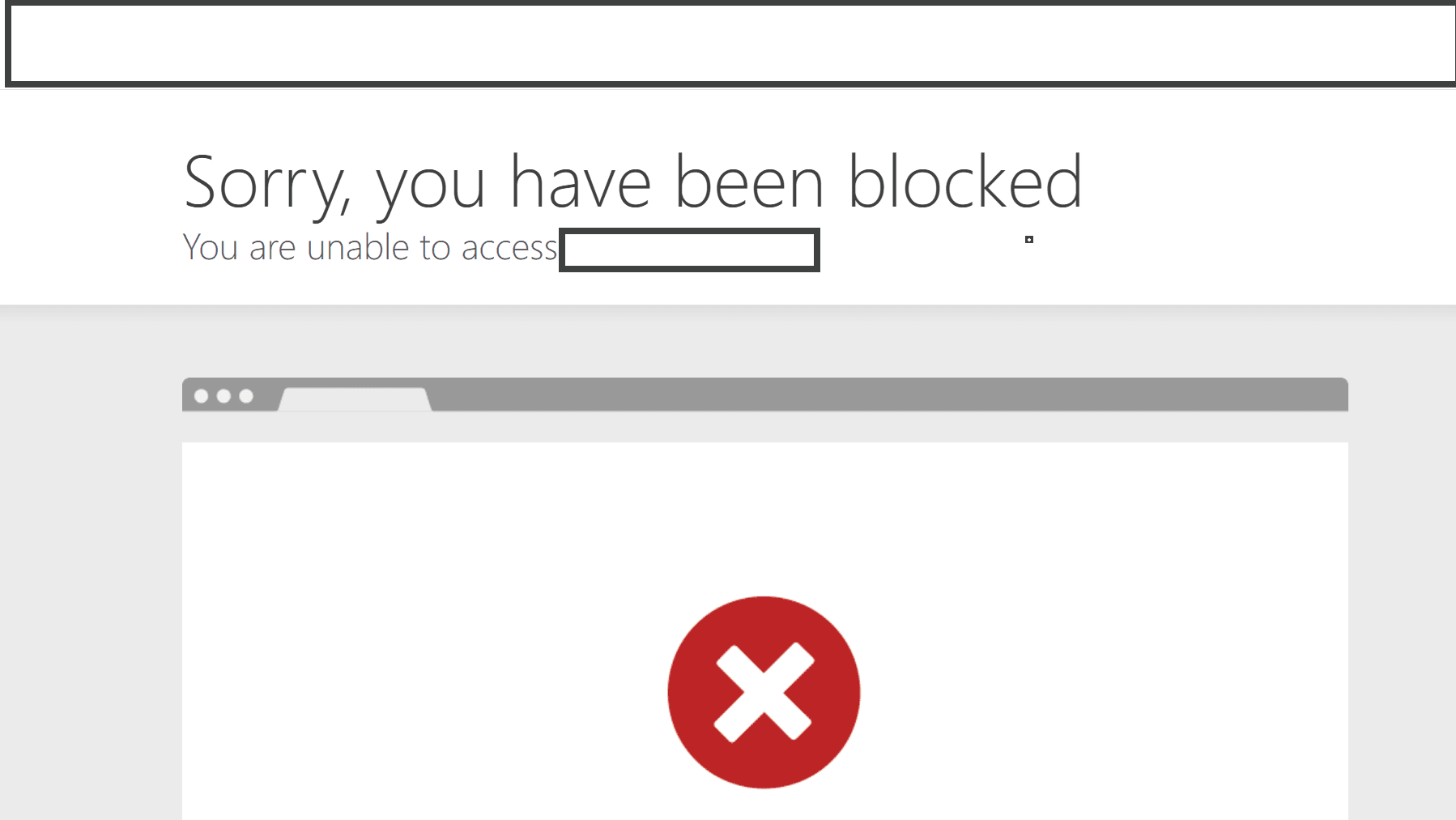
At this stage, the block only showed that one request pattern matched a detection rule. It did not prove that the application handled untrusted input safely.
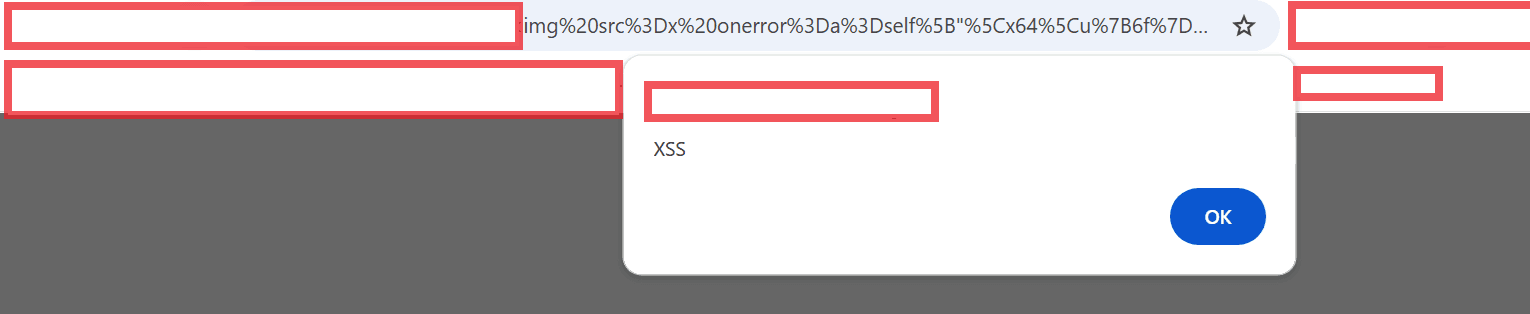
After further testing, a different input variation still resulted in JavaScript execution in the browser.